This topic for the IT professional describes the system architecture that supports smart cards in the Windows operating system, including credential provider architecture and the smart card subsystem architecture.
Authentication is a process for verifying the identity of an object or person. When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an imposter.
In a networking context, authentication is the act of proving identity to a network application or resource. Typically, identity is proven by a cryptographic operation that uses a key only the user knows (such as with public key cryptography), or a shared key. The server side of the authentication exchange compares the signed data with a known cryptographic key to validate the authentication attempt. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable.
For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. This topic includes information about:
The following table lists the components that are included in the interactive sign-in architecture:
| Component | Description |
|---|---|
| Winlogon | Provides an interactive sign-in infrastructure. |
| Logon UI | Provides interactive UI rendering. |
| Credential providers (password and smart card) | Describes credential information and serializing credentials. |
| Local Security Authority (LSA) | Processes sign-in credentials. |
| Authentication packages | Includes NTLM and the Kerberos protocol. Communicates with server authentication packages to authenticate users. |
Interactive sign-in in Windows begins when the user presses CTRL+ALT+DEL. The CTRL+ALT+DEL key combination is called a secure attention sequence (SAS). To keep other programs and processes from using it, Winlogon registers this sequence during the boot process.
After receiving the SAS, the UI then generates the sign-in tile from the information received from the registered credential providers. The following graphic shows the architecture for credential providers in the Windows operating system.
Typically, a user who signs in to a computer by using a local account or a domain account must enter a user name and password. These credentials are used to verify the user's identity. For smart card sign-in, a user's credentials are contained on the smart card's security chip. A smart card reader lets the computer interact with the security chip on the smart card. When users sign in with a smart card, they enter a personal identification number (PIN) instead of a user name and password.
Credential providers are in-process COM objects that run on the local system and are used to collect credentials. The Logon UI provides interactive UI rendering, Winlogon provides interactive sign-in infrastructure, and credential providers work with both of these components to help gather and process credentials.
Winlogon instructs the Logon UI to display credential provider tiles after it receives an SAS event. The Logon UI queries each credential provider for the number of credentials it wants to enumerate. Credential providers have the option of specifying one of these tiles as the default. After all providers have enumerated their tiles, the Logon UI displays them to the user. The user interacts with a tile to supply the proper credentials. The Logon UI submits these credentials for authentication.
Combined with supporting hardware, credential providers can extend the Windows operating system to enable users to sign in by using biometrics (for example, fingerprint, retinal, or voice recognition), password, PIN, smart card certificate, or any custom authentication package. Enterprises and IT professionals can develop and deploy custom authentication mechanisms for all domain users, and they may explicitly require users to use this custom sign-in mechanism.
Credential providers are not enforcement mechanisms. They are used to gather and serialize credentials. The LSA and authentication packages enforce security.
Credential providers can be designed to support single sign-in (SSO). In this process, they authenticate users to a secure network access point (by using RADIUS and other technologies) for signing in to the computer. Credential providers are also designed to support application-specific credential gathering, and they can be used for authentication to network resources, joining computers to a domain, or to provide administrator consent for User Account Control (UAC).
Multiple credential providers can coexist on a computer.
Credential providers must be registered on a computer running Windows, and they're responsible for:
The Credential Provider API does not render the UI. It describes what needs to be rendered.
Only the password credential provider is available in safe mode.
The smart card credential provider is available in safe mode during networking.
Vendors provide smart cards and smart card readers, and in many cases the vendors are different for the smart card and the smart card reader. Drivers for smart card readers are written to the Personal Computer/Smart Card (PC/SC) standard. Each smart card must have a Cryptographic Service Provider (CSP) that uses the CryptoAPI interfaces to enable cryptographic operations, and the WinSCard APIs to enable communications with smart card hardware.
The following graphic shows the relationship between the CryptoAPI, CSPs, the Smart Card Base Cryptographic Service Provider (Base CSP), and smart card minidrivers.
Smart card architecture uses caching mechanisms to help streamlining operations and to improve a user's access to a PIN.
Each CSP implements the current smart card data cache separately. The Base CSP implements a robust caching mechanism that allows a single process to minimize smart card I/O operations.
The existing global cache works as follows:
Three types of objects or data are cached by the CSP: pins (for more information, see PIN caching), certificates, and files. If any of the cached data changes, the corresponding object is read from the smart card in successive operations. For example, if a file is written to the smart card, the CSP cache becomes out-of-date for the files, and other processes read the smart card at least once to refresh their CSP cache.
The global data cache is hosted in the Smart Cards for Windows service. Windows includes two public smart card API calls, SCardWriteCache and SCardReadCache. These API calls make global data caching functionality available to applications. Every smart card that conforms to the smart card minidriver specification has a 16-byte card identifier. This value is used to uniquely identify cached data that pertains to a given smart card. The standard Windows GUID type is used. These APIs allow an application to add data to and read data from the global cache.
The PIN cache protects the user from entering a PIN every time the smart card is unauthenticated. After a smart card is authenticated, it will not differentiate among host-side applications—any application can access private data on the smart card.
To mitigate this, the smart card enters an exclusive state when an application authenticates to the smart card. However, this means that other applications can't communicate with the smart card and will be blocked. Therefore, such exclusive connections are minimized. The issue is that a protocol (such as the Kerberos protocol) requires multiple signing operations. Therefore, the protocol requires exclusive access to the smart card over an extended period, or it requires multiple authentication operations. This is where the PIN cache is used to minimize exclusive use of the smart card without forcing the user to enter a PIN multiple times.
The following example illustrates how this works. In this scenario, there are two applications: Outlook and Internet Explorer. The applications use smart cards for different purposes.
The Base CSP internally maintains a per-process cache of the PIN. The PIN is encrypted and stored in memory. The functions that are used to secure the PIN are RtlEncryptMemory, RtlDecryptMemory, and RtlSecureZeroMemory, which will empty buffers that contained the PIN.
The following sections in this article describe how Windows uses the smart card architecture to select the correct smart card reader software, provider, and credentials for a successful smart card sign-in:
In response to a CryptAcquireContext call in CryptoAPI, the Base CSP tries to match the container that the caller specifies to a specific smart card and reader. The caller can provide a container name with varying levels of specificity, as shown in the following table, and sorted from most-specific to least-specific requests.
Similarly, in response to a NCryptOpenKey call in CNG, the smart card KSP tries to match the container the same way, and it takes the same container format, as shown in the following table.
Before opening a key by using the smart card KSP, a call to NCryptOpenStorageProvider ( MS_SMART_CARD_KEY_STORAGE_PROVIDER ) must be made.
| Type | Name | Format |
|---|---|---|
| I | Reader Name and Container Name | \. |
| II | Reader Name and Container Name (NULL) | \. |
| III | Container Name Only | |
| IV | Default Container (NULL) Only | NULL |
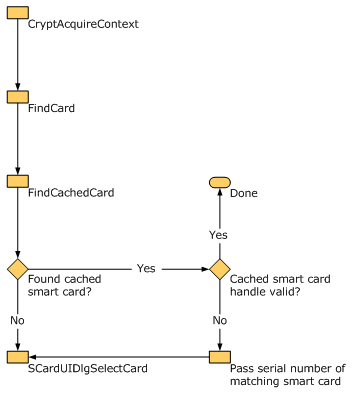
The Base CSP and smart card KSP cache smart card handle information about the calling process and about the smart cards the process has accessed. When searching for a smart card container, the Base CSP or smart card KSP first checks its cache for the process. If the cached handle is invalid or no match is found, the SCardUIDlg API is called to get the card handle.
The following three container operations can be requested by using CryptAcquireContext:
The heuristics that are used to associate a cryptographic handle with a particular smart card and reader are based on the container operation requested and the level of container specification used.
The following table shows the restrictions for the container creation operation.
| Specification | Restriction |
|---|---|
| No silent context | Key container creation must always be able to show UI, such as the PIN prompt. |
| No overwriting existing containers | If the specified container already exists on the chosen smart card, choose another smart card or cancel the operation. |
The following table shows the context flags used as restrictions for the container creation operation.
| Flag | Description |
|---|---|
| CRYPT_SILENT | No UI can be displayed during this operation. |
| CRYPT_MACHINE_KEYSET | No cached data should be used during this operation. |
| CRYPT_VERIFYCONTEXT | Only public data can be accessed on the smart card. |
In addition to container operations and container specifications, you must consider other user options, such as the CryptAcquireContext flags, during smart card selection.
The CRYPT_SILENT flag cannot be used to create a new container.
Applications can call the Base CSP with CRYPT_DEFAULT_CONTAINER_OPTIONAL , set the PIN in silent context, and then create a new container in silent context. This operation occurs as follows:
In some of the following scenarios, the user can be prompted to insert a smart card. If the user context is silent, this operation fails and no UI is displayed. Otherwise, in response to the UI, the user can insert a smart card or select Cancel. If the user cancels the operation, the operation fails. The flow chart shows the selection steps performed by the Windows operating system.
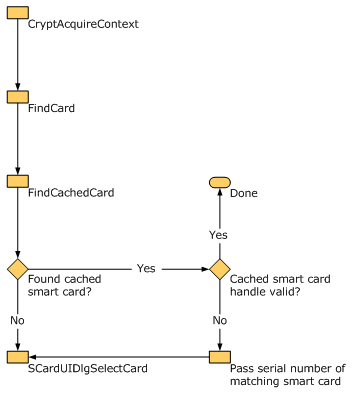
In general, smart card selection behavior is handled by the SCardUIDlgSelectCard API. The Base CSP interacts with this API by calling it directly. The Base CSP also sends callback functions that have the purpose of filtering and matching candidate smart cards. Callers of CryptAcquireContext provide smart card matching information. Internally, the Base CSP uses a combination of smart card serial numbers, reader names, and container names to find specific smart cards.
Each call to SCardUI * may result in additional information read from a candidate smart card. The Base CSP smart card selection callbacks cache this information.
For type I and type II container specification levels, the smart card selection process is less complex because only the smart card in the named reader can be considered a match. The process for matching a smart card with a smart card reader is:
For container specification levels III and IV, a broader method is used to match an appropriate smart card with a user context, because multiple cached smart cards might meet the criteria provided.
This operation requires that you use the smart card with the Base CSP.
This operation requires that you use the smart card with the Base CSP.
This operation requires that you use the smart card with the Base CSP.
If the PIN isn't cached, no CRYPT_SILENT is allowed for the container creation because the user must be prompted for a PIN, at a minimum.
For other operations, the caller may be able to acquire a verify context against the default container CRYPT_DEFAULT_CONTAINER_OPTIONAL and then make a call with CryptSetProvParam to cache the user PIN for subsequent operations.
The following diagram shows the Cryptography architecture that is used by the Windows operating system.
The API definitions are located in WinCrypt.h and WinSCard.h.
| Property | Description |
|---|---|
| PP_USER_CERTSTORE | - Used to return an HCERTSTORE that contains all user certificates on the smart card - Read-only (used only by CryptGetProvParam ) - Caller responsible for closing the certificate store - Certificate encoded using PKCS_7_ASN_ENCODING or X509_ASN_ENCODING - CSP should set KEY_PROV_INFO on certificates - Certificate store should be assumed to be an in-memory store - Certificates should have a valid CRYPT_KEY_PROV_INFO as a property |
| PP_ROOT_CERTSTORE | - Read and Write (used by CryptGetProvParam and CryptSetProvParam ) - Used to write a collection of root certificates to the smart card or return HCERTSTORE , which contains root certificates from the smart card - Used primarily for joining a domain by using a smart card - Caller responsible for closing the certificate store |
| PP_SMARTCARD_READER | - Read-only (used only by CryptGetProvParam ) - Returns the smart card reader name as an ANSI string that is used to construct a fully qualified container name (that is, a smart card reader plus a container) |
| PP_SMARTCARD_GUID | - Return smart card GUID (also known as a serial number), which should be unique for each smart card - Used by the certificate propagation service to track the source of a root certificate |
| PP_UI_PROMPT | - Used to set the search string for the SCardUIDlgSelectCard card insertion dialog box - Persistent for the entire process when it's set - Write-only (used only by CryptSetProvParam ) |
Cryptographic Service Providers (CSPs), including custom smart card CSPs, continue to be supported but this approach isn't recommended. Using the existing Base CSP and smart card KSP with the smart card minidriver model for smart cards provides significant benefits in terms of performance, and PIN and data caching. One minidriver can be configured to work under CryptoAPI and CNG layers. This provides benefits from enhanced cryptographic support, including elliptic curve cryptography and AES.
If a smart card is registered by a CSP and a smart card minidriver, the one that was installed most recently will be used to communicate with the smart card.
CSPs and KSPs are meant to be written only if specific functionality isn't available in the current smart card minidriver architecture. For example, the smart card minidriver architecture supports hardware security modules, so a minidriver could be written for a hardware security module, and a CSP or KSP may not be required unless it's needed to support algorithms that aren't implemented in the Base CSP or smart card KSP.
For more information about how to write a smart card minidriver, CSP, or KSP, see Smart Card Minidrivers.